4 Ways IT must Change to Protect your Business
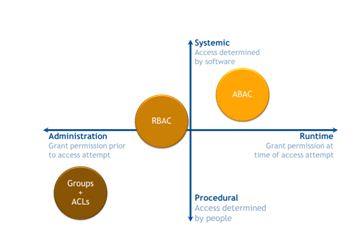
By E.K. Koh, VP of Solutions at NextLabs It’s not your perimeter. It’s not your applications. In an age where there is no perimeter, where data moves from application to application, from servers to desktops to tablets and smart phones that the company does not even own, managing security at the perimeter or application is … More 4 Ways IT must Change to Protect your Business